AI synthetic imagery in the NSFW domain: what you need to know
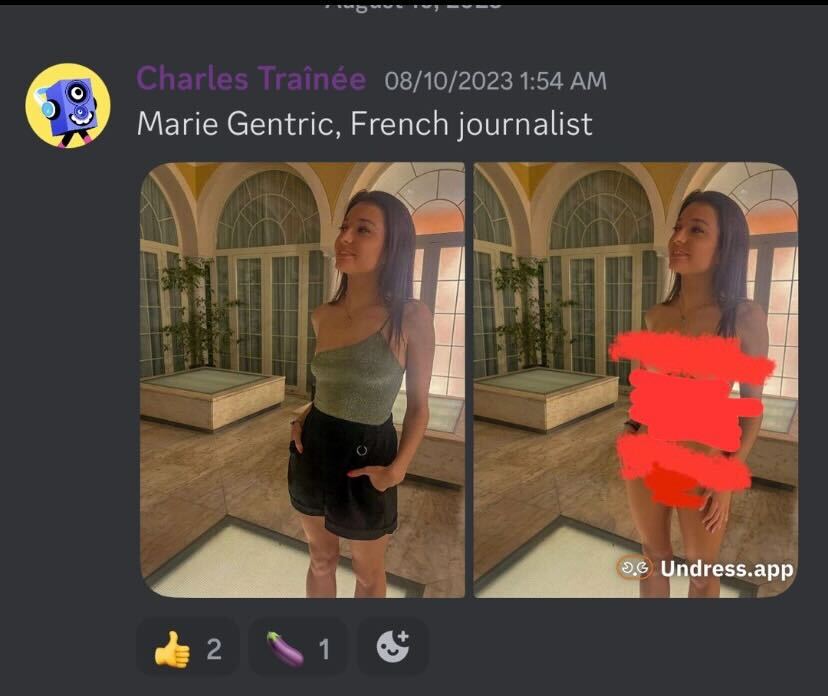
Sexualized deepfakes and “undress” images are currently cheap to create, hard to identify, and devastatingly convincing at first look. The risk isn’t theoretical: artificial intelligence-driven clothing removal tools and online naked generator services get utilized for harassment, coercion, and reputational harm at scale.
The space moved far from the early initial undressing app era. Current adult AI tools—often branded like AI undress, synthetic Nude Generator, and virtual “AI girls”—promise believable nude images through a single image. Even when their output stays perfect, it’s convincing enough to trigger panic, blackmail, plus social fallout. Across platforms, people discover results from services like N8ked, clothing removal tools, UndressBaby, nude AI platforms, Nudiva, and related tools. The tools vary in speed, quality, and pricing, however the harm process is consistent: unauthorized imagery is created and spread faster than most affected individuals can respond.
Handling this requires two parallel skills. First, learn to detect nine common warning signs that betray artificial manipulation. Next, have a action plan that focuses on evidence, fast reporting, and safety. What follows is a real-world, field-tested playbook used among moderators, trust and safety teams, and digital forensics experts.
How dangerous have NSFW deepfakes become?
Simple usage, realism, and viral spread combine to raise the risk assessment. The “undress tool” category is remarkably simple, and digital platforms can distribute a single manipulated image to thousands among users before a takedown lands.
Low friction constitutes the core problem. A single selfie can be extracted from a page and fed into a Clothing Undressing Tool within seconds; some porngen art generators also automate batches. Results is inconsistent, however extortion doesn’t require photorealism—only credibility and shock. Outside coordination in private chats and data dumps further increases reach, and numerous hosts sit away from major jurisdictions. This result is rapid whiplash timeline: production, threats (“send extra photos or we share”), and distribution, often before a victim knows where one might ask for support. That makes recognition and immediate triage critical.
Red flag checklist: identifying AI-generated undress content
Most undress deepfakes display repeatable tells within anatomy, physics, plus context. You won’t need specialist software; train your eye on patterns where models consistently get wrong.
First, check for edge artifacts and boundary problems. Clothing lines, ties, and seams frequently leave phantom imprints, with skin appearing unnaturally smooth when fabric should might have compressed it. Adornments, especially neck accessories and earrings, could float, merge into skin, or disappear between frames of a short clip. Tattoos and scars are frequently absent, blurred, or displaced relative to base photos.
Second, scrutinize lighting, shadows, along with reflections. Shadows under breasts or across the ribcage might appear airbrushed while being inconsistent with such scene’s light direction. Reflections in reflective surfaces, windows, or shiny surfaces may reveal original clothing while the main figure appears “undressed,” a high-signal inconsistency. Light highlights on body sometimes repeat in tiled patterns, one subtle generator fingerprint.
Third, check texture quality and hair natural behavior. Skin pores may appear uniformly plastic, displaying sudden resolution changes around the body. Body hair and fine flyaways by shoulders or the neckline often blend into the surroundings or have haloes. Fine details that should cover the body might be cut short, a legacy artifact from segmentation-heavy pipelines used by many undress generators.
Fourth, assess proportions and consistency. Tan lines may be absent or painted on. Breast shape and natural positioning can mismatch physical characteristics and posture. Hand pressure pressing into the body should compress skin; many AI images miss this natural indentation. Clothing remnants—like a sleeve edge—may embed into the body in impossible manners.
Fifth, read the scene context. Crops tend to avoid challenging areas such as armpits, hands on skin, or where clothing meets skin, concealing generator failures. Environmental logos or text may warp, and EXIF metadata gets often stripped or shows editing applications but not original claimed capture equipment. Reverse image checking regularly reveals source source photo dressed on another location.
Next, evaluate motion signals if it’s video. Respiratory motion doesn’t move body torso; clavicle and chest motion lag background audio; and natural laws of hair, accessories, and fabric fail to react to movement. Face swaps sometimes blink at odd intervals compared with natural human eye closure rates. Room acoustics and voice quality can mismatch displayed visible space while audio was synthesized or lifted.
Seventh, examine duplicates along with symmetry. AI favors symmetry, so you may spot duplicated skin blemishes reflected across the figure, or identical creases in sheets visible on both areas of the image. Background patterns occasionally repeat in artificial tiles.
Next, look for user behavior red flags. Recent profiles with sparse history that suddenly post NSFW “leaks,” aggressive DMs demanding payment, or unclear storylines about when a “friend” obtained the media indicate a playbook, instead of authenticity.
Ninth, focus on consistency across a set. If multiple “images” depicting the same subject show varying body features—changing moles, disappearing piercings, or inconsistent room details—the likelihood you’re dealing encountering an AI-generated series jumps.
What’s your immediate response plan when deepfakes are suspected?
Preserve evidence, remain calm, and function two tracks at once: removal and containment. The first hour matters more versus the perfect message.
Start with documentation. Capture full-page screenshots, the URL, timestamps, profile IDs, and any IDs in the URL bar. Save complete messages, including demands, and record monitor video to demonstrate scrolling context. Don’t not edit such files; store them in a safe folder. If coercion is involved, do not pay and do not bargain. Blackmailers typically intensify efforts after payment because it confirms participation.
Next, trigger platform plus search removals. Report the content through “non-consensual intimate media” or “sexualized deepfake” where available. File intellectual property takedowns if such fake uses individual likeness within some manipulated derivative from your photo; numerous hosts accept these even when this claim is contested. For ongoing protection, use a hash-based service like blocking services to create a hash of personal intimate images plus targeted images) allowing participating platforms can proactively block future uploads.
Notify trusted contacts while the content involves your social connections, employer, plus school. A brief note stating this material is artificial and being handled can blunt rumor-based spread. If the subject is any minor, stop everything and involve legal enforcement immediately; manage it as emergency child sexual harm material handling while do not circulate the file further.
Finally, consider legal routes where applicable. Depending on jurisdiction, you may have cases under intimate content abuse laws, identity theft, harassment, defamation, and data protection. One lawyer or regional victim support agency can advise about urgent injunctions along with evidence standards.
Removal strategies: comparing major platform policies
Most major platforms forbid non-consensual intimate imagery and deepfake adult material, but scopes plus workflows differ. Move quickly and submit on all platforms where the material appears, including copies and short-link hosts.
| Platform | Main policy area | Where to report | Typical turnaround | Notes |
|---|---|---|---|---|
| Meta platforms | Non-consensual intimate imagery, sexualized deepfakes | In-app report + dedicated safety forms | Same day to a few days | Supports preventive hashing technology |
| X social network | Unauthorized explicit material | Profile/report menu + policy form | 1–3 days, varies | Appeals often needed for borderline cases |
| TikTok | Explicit abuse and synthetic content | Application-based reporting | Hours to days | Blocks future uploads automatically |
| Unwanted explicit material | Report post + subreddit mods + sitewide form | Varies by subreddit; site 1–3 days | Pursue content and account actions together | |
| Alternative hosting sites | Anti-harassment policies with variable adult content rules | Contact abuse teams via email/forms | Highly variable | Use DMCA and upstream ISP/host escalation |
Available legal frameworks and victim rights
The law remains catching up, and you likely possess more options than you think. People don’t need to prove who created the fake to request removal through many regimes.
In the UK, distributing pornographic deepfakes lacking consent is one criminal offense via the Online Protection Act 2023. In the EU, current AI Act requires labeling of AI-generated content in certain contexts, and privacy laws like data protection regulations support takedowns when processing your representation lacks a legal basis. In United States US, dozens across states criminalize unauthorized pornography, with many adding explicit synthetic content provisions; civil claims for defamation, violation upon seclusion, plus right of publicity often apply. Many countries also provide quick injunctive protection to curb spread while a case proceeds.
If an undress photo was derived via your original image, copyright routes might help. A copyright notice targeting the derivative work and the reposted original often leads into quicker compliance from hosts and search engines. Keep all notices factual, prevent over-claiming, and mention the specific web addresses.
Where service enforcement stalls, escalate with appeals referencing their stated bans on “AI-generated porn” and “non-consensual personal imagery.” Persistence proves crucial; multiple, well-documented reports outperform one general complaint.
Reduce your personal risk and lock down your surfaces
You won’t eliminate risk completely, but you may reduce exposure and increase your control if a issue starts. Think within terms of material that can be scraped, how it might be remixed, along with how fast individuals can respond.
Secure your profiles through limiting public high-resolution images, especially direct, bright selfies that strip tools prefer. Explore subtle watermarking for public photos plus keep originals archived so you will prove provenance during filing takedowns. Check friend lists plus privacy settings within platforms where strangers can DM and scrape. Set establish name-based alerts across search engines along with social sites for catch leaks promptly.
Create some evidence kit well advance: a template log for web addresses, timestamps, and profile IDs; a safe online folder; and one short statement you can send for moderators explaining this deepfake. If anyone manage brand plus creator accounts, consider C2PA Content verification for new posts where supported to assert provenance. For minors in your care, lock away tagging, disable unrestricted DMs, and teach about sextortion approaches that start with “send a personal pic.”
At work or educational settings, identify who oversees online safety problems and how rapidly they act. Setting up a response route reduces panic along with delays if people tries to spread an AI-powered artificial intimate photo claiming it’s your image or a coworker.
Did you know? Four facts most people miss about AI undress deepfakes
Most AI-generated content online remains sexualized. Multiple independent studies from past past few research cycles found that such majority—often above most in ten—of discovered deepfakes are adult and non-consensual, that aligns with findings platforms and investigators see during content moderation. Hashing works without sharing individual image publicly: initiatives like StopNCII create a digital fingerprint locally and only share the fingerprint, not the image, to block re-uploads across participating websites. EXIF file data rarely helps once content is shared; major platforms strip it on upload, so don’t depend on metadata for provenance. Content verification standards are gaining ground: C2PA-backed “Content Credentials” can embed signed edit history, making it more straightforward to prove material that’s authentic, but implementation is still inconsistent across consumer apps.
Quick response guide: detection and action steps
Pattern-match for the 9 tells: boundary irregularities, lighting mismatches, surface quality and hair problems, proportion errors, background inconsistencies, motion/voice mismatches, mirrored repeats, suspicious account behavior, along with inconsistency across the set. When you see two and more, treat this as likely artificial and switch to response mode.
Capture evidence without resharing this file broadly. Flag content on every host under non-consensual personal imagery or explicit deepfake policies. Use copyright and data protection routes in parallel, and submit one hash to trusted trusted blocking provider where available. Notify trusted contacts using a brief, accurate note to cut off amplification. While extortion or underage persons are involved, contact to law enforcement immediately and refuse any payment plus negotiation.
Most importantly all, act rapidly and methodically. Strip generators and web-based nude generators rely on shock and speed; your benefit is a systematic, documented process where triggers platform systems, legal hooks, and social containment as a fake might define your reputation.
For clarity: references about brands like specific services like N8ked, DrawNudes, strip applications, AINudez, Nudiva, and PornGen, and similar AI-powered undress app or Generator systems are included when explain risk patterns and do not endorse their deployment. The safest approach is simple—don’t participate with NSFW synthetic content creation, and learn how to address it when synthetic media targets you plus someone you care about.
